Blog: Cybersecurity
Filter By

Cybersecurity
Flight Attendant to Tech Specialist: Tyler Blocker's Career Transformation
Learn how Tyler Blocker, a former flight attendant and active personal trainer with a passion for technology, successfully transitioned into a tech career after training in our online Cybersecurity Bootcamp.
Read more

Cybersecurity
Information Security vs. Cybersecurity: What's the Difference?
What does it take to protect companies from data breaches? Whether you go into information security or cybersecurity, these skills are in high demand.
Read more
Cybersecurity
How to Become a Penetration Tester
Cybersecurity experts are needed to find exploits in businesses’ systems. Learn how to become a penetration tester and protect companies with “ethical hacking.”
Read more

Cybersecurity
How to Become a Cybersecurity Analyst
Businesses without adequate security are targets for cyberattacks. Discover how to become a cybersecurity analyst, and enter one of today’s hottest fields.
Read more

Cybersecurity
7 Types of Cybersecurity You Should Know
Because cyber threats come in many forms, so does cybersecurity. Find out about seven types of cybersecurity and the different ways they protect networks.
Read more

Cybersecurity
Cybersecurity Horror Stories to Tell In the Dark
In this spirit of Halloween, we’ve created 5 hypothetical horror stories to help inform, entertain, and inspire you to secure your data this season and beyond. Read on to learn how cybersecurity best practices can help you prevent a harrowing tale of your own this Halloween.
Read more

Cybersecurity
Internet Security Tips for the Back-to-School Season
Between extended time away from home, seasonal sales, and the long Labor Day weekend, the back-to-school season in the U.S. is a great time to ensure your accounts, devices, and data are protected.
Read more
Cybersecurity
Most Common Phishing Lures in Every State
We explored the most common phishing lures in each U.S. state, as well as the most commonly impersonated organizations in digital scams.
Read more
Cybersecurity
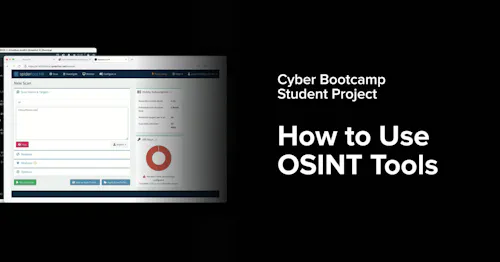
Cyber Bootcamp Student Project: How to Use OSINT Tools
Cybersecurity Bootcamp students learn by doing throughout the project-based curriculum. Watch an example of a completed cybersecurity bootcamp capstone project about open-source intelligence tools.
Read more

Cybersecurity
Cybersecurity Bootcamp Student Projects: Mitigating Cyberthreats
Cybersecurity bootcamp students complete a Capstone Project to demonstrate what they’ve learned and offer real-world solutions to potential cyberattacks. Watch a few cybersecurity projects completed and presented by bootcamp students.
Read more
Cybersecurity
Overcoming Imposter Syndrome to Pursue a Cyber Career
Although he enrolled with limited tech experience and skills, Virginia Tech Cybersecurity Bootcamp graduate Kelly Johnson is now confident in his job readiness. Follow his journey.
Read more

Cybersecurity
From Beginner to Cybersecurity Analyst: Kennedy Arnold's Journey with Virginia Tech
Kennedy Arnold is a graduate of the Virginia Tech Cybersecurity Bootcamp who successfully transitioned from beginner to job-ready Cybersecurity professional. Here's her journey of achieving career success through the bootcamp.
Read more